...
| Provider Name | This name will be displayed in the Authentication dialog in SignAnyWhere Viewer, so make sure it identifies your organization. e.g.: Video Ident with LiveId+ |
| Redirect Url | This is already set and has to be white listed on LIP OAuthWrapper. We already provided this URL in the request in Step 2. |
Client Id | your "Application (client) ID" from Step 2 |
| Client Secret: | your secret's value from Step 2 |
| Scope: | |
| Authorization URI: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus/api/authorize |
| Token URI: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus/api/getToken |
| Logout URI: | can be blank |
| JWKS URI: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus/Jwk/getJwks |
| Issuer: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus |
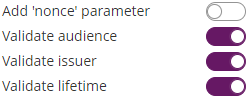
| On-Off Sliders: |
And then configure the following field mappings:
...
| Provider Name | This name will be displayed in the Authentication dialog in SignAnyWhere Viewer, so make sure it identifies your organization. e.g.: SmartIdent |
| Redirect Url | This is already set and has to be white listed on SignD side. We already provided this URL in the request in Step 1. |
Client Id | your "Application (client) ID" from Step 1 |
| Client Secret: | your secret's value from Step 1 |
| Scope: | openid flat |
| Authorization URI: | https://openid.signd.id/v1/oauth/authorize |
| Token URI: | |
| Logout URI: | can be blank |
| JWKS URI: | |
| Issuer: | |
| On-Off Sliders: |
And then configure the following field mappings:
...
| Client ID: | your Client ID |
| Client Secret: | your Client Secret |
| Scope: | openid profile |
| Authorization URI: | https://eid2.oesterreich.gv.at/auth/idp/profile/oidc/authorize |
| Token URI: | https://eid2.oesterreich.gv.at/auth/idp/profile/oidc/token |
| Logout URI: | |
| JWKS URI: | |
| Issuer: | https://eid2.oesterreich.gv.at |
| On-Off Sliders: |
The URIs are documented in https://eid.egiz.gv.at/anbindung/direkte-anbindung/anbindung-oidc/ - if above's URIs don't work, check if there was an update on this page.
...
| Provider Name | If "Share on login page" is enabled, this name will be displayed on the login page, so make sure it identifies your organization. e.g.: MyNamirial for <Organization name> |
| Direct access url | If "Share on login page" is disabled, this link is needed to login to eSignAnyWhere with OAuth 2.0. Make sure you bookmark this link. |
| Redirect Url | This is already set and has to be white listed on MyNamirial. We already provided this URL in the request in Step 1. |
Client Id | your "Application (client) ID" from Step 1 |
| Client Secret: | your secret's value from Step 1 |
| Scope: | openid email |
| Authorization URI: | your authorization_endpoint from Step 2 or simply (for production instance of MyNamirial)https://auth.namirial.app/realms/namirial/protocol/openid-connect/auth |
| Token URI: | your token_endpoint from Step 2 or simply (for production instance of MyNamirial)https://auth.namirial.app/realms/namirial/protocol/openid-connect/token |
| Logout URI: | (Optional - can be blank) your end_session from Step 2 or simply (for production instance of MyNamirial)https://auth.namirial.app/realms/namirial/protocol/openid-connect/logout |
| Share on login page | Depending on the server settings this property might not be visible to you. If enabled your provider name will show up on the login page. |
| JWKS URI: | your jwks_uri from Step 2 or simply (for production instance of MyNamirial) |
| Issuer: | your https://auth.namirial.app/realms/namirial |
| On-Off Sliders: | |
| Field Mappings: | Click on "Add field" and enter "email". Select rule "Validate" and map it to "User Email Address" |
...