...
| Client ID: | your Linked Client ID |
| Client Secret: | your LinkedIn Client Secret |
| Scope: | r_basicprofile r_emailaddress |
| Authorization URI: | https://www.linkedin.com/oauth/v2/authorization |
| Token URI: | https://www.linkedin.com/oauth/v2/accessToken |
| Logout URI: | https://www.linkedin.com |
| Ressource Parameter: | oauth2_access_token |
| Ressource URI: | https://api.linkedin.com/v1/people/~:(id,firstName,lastName,headline,email-address)?format=json |
Authenticate with Facebook
...
The configured Ressource URI returns a JSON object with the specified parameter. These parameters can be defined in the fields to force a specific LinkedIn user to authenticate (e.g. email address). HINT: to see what data is returned in the Ressource URI send yourself an envelope and have a look in the audit trail. It contains the returned object with its parameter. Note: Parameter in Ressource URI of LinkedIn is not the same in the result (email vs. emailAddress).
The Ressource URI will return data of the profile. With the “Graph API Explorer” you can build and test your own profile requests. With the optional configuration of “Fields” you can define fields, which are checked for authentication. So you can force a specific user (e.g. identified via email, id or birthdate) to authenticate. Other users are not accepted.
...
Please see the following figure for more information about the configuration in eSAW:
(Hint: in some older product versions, this settings had been located in Settings-Organization, section "OAuth Settings").
...
If authentication was successful, the signer will be logged in and SAW Viewer will grant access to the document.
After a successful login, the granted access for the OAuth Application is shown in Settings->Api Tokens and Apps in the section Apps and Connectors:
For more information about the signing process in eSAW please also see the next video:
...
| Provider Name | This name will be displayed in the Authentication dialog in SignAnyWhere Viewer, so make sure it identifies your organization. e.g.: Video Ident with LiveId+ |
| Redirect Url | This is already set and has to be white listed on LIP OAuthWrapper. We already provided this URL in the request in Step 2. |
Client Id | your "Application (client) ID" from Step 2 |
| Client Secret: | your secret's value from Step 2 |
| Scope: | |
| Authorization URI: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus/api/authorize |
| Token URI: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus/api/getToken |
| Logout URI: | can be blank |
| JWKS URI: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus/Jwk/getJwks |
| Issuer: | https://<your-esaw-instance>/OAuthWrapperLiveIdPlus |
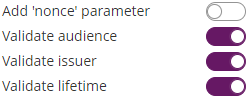
| On-Off Sliders: |
And then configure the following field mappings:
...
After setting these values, the JWT and field mapping configuraiton should look similar to the following screenshot.
Please note that the disposable certificate identification number will be updated with this configuration. If you want to override the identification number as it is shown in the configuration please also make sure to add a disposable certificate for the signer.
Production Environment - USP Service "E-ID Serviceprovider"
...
Please also see the next figures for the OAuth2 configuration and the JWT configuration:
Add the following field mapping configurations:
...